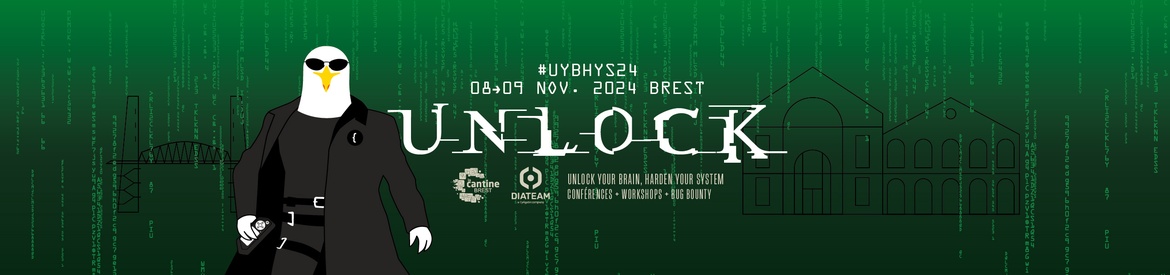
Unlock your Brain, Harden your System
https://www.unlockyourbrain.bzh
L'événement de sécurité numérique le plus à l'Ouest !
La 9ème édition de "Unlock Your Brain, Harden Your System" se tiendra le vendredi 8 et le samedi 9 novembre 2024 à Brest ⋅ France
Programme : https://www.unlockyourbrain.bzh/programme/
-
Vendredi 8 nov de 10h00 à 18h : dédié aux workshops
-
Vendredi 8 nov après-midi à 14h00 à 19h00 : Bug Bounty
-
Samedi 9 nov 2023 de 9h00 à 18h30
journée de conférences - déjeuner inclus
social event : Closing Party de 19h00 à 00h00
Cet événement est organisé conjointement par la Cantine numérique Brest et DIATEAM
Workshops: CCI Brest, 1 place du 19e RI, 29200 Brest
Bug Bounty: Salle des Records, Marina du Château, 29200 Brest
Conference: Javouhey High School, rue de l'Église, 29200 Brest
jusqu’à
Début :
Fin :
Ajouter à l'Agenda