Security release 4.17.1 of pretix
Today, we've internally discovered a security issue inside pretix. We therefore just released versions 4.17.1, 4.16.1, and 4.15.1 of pretix that fix this problem. It is strongly recommended that you update your installation as soon as possible.
If you are a customer of our pretix Hosted service, you will receive an email with further information before the end of the day if we believe you could be affected. You can also check yourself whether you are affected using the steps below.
#1: Incorrect session validation during OAuth authorization [HIGH]
CVE ID: CVE-2023-27891
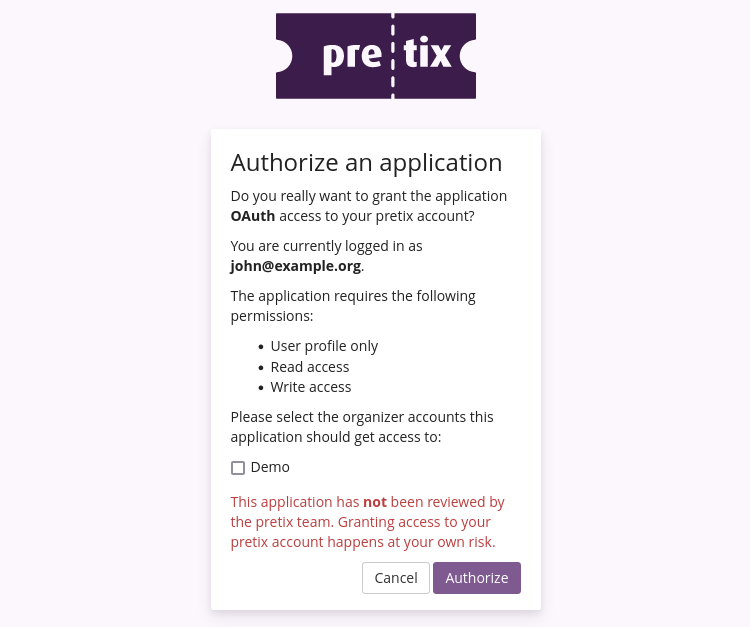
pretix allows third-party applications to integrate with our API using OAuth authorization. This means that the external application receives access to the data stored inside pretix that you have access to. If such an application requests access to your account, you will see a confirmation prompt similar to this one:
The security problem that we found is that this prompt allowed you to confirm access to the third-party application even though your session has already timed out.
Specifically, pretix usually requires a new login after 12 hours (unless the user requested to be logged in for longer). However, the authorization dialog kept working after those 12 hours (up to the general session limit of 14 days of inactivity).
Theoretically, this would allow an attacker with access to your device to connect a third-party application even though you believe you have been automatically logged out of the system. Note that access to a browser (or session cookie) with a recent valid login into the system is required for the security problem to be exploitable, it is not possible for a remote attacker to use this to get access to random accounts.
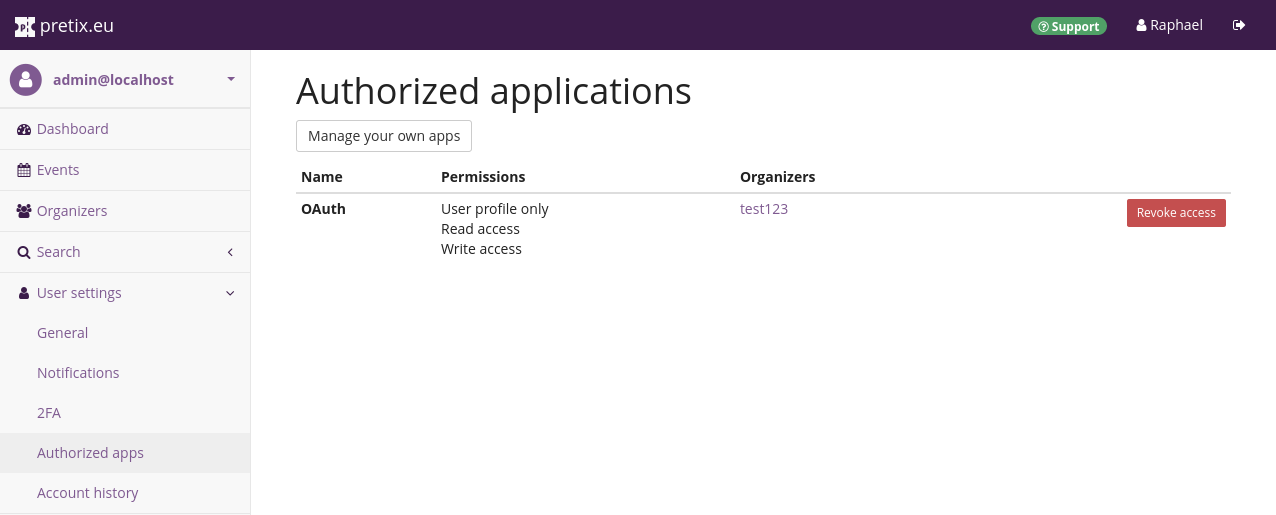
It is unlikely that this happened without anyone noticing, since every time a new application is authorized for an account, an email is sent to the user. However, since it is possible that this email might not have been understood to have priority it has, we recommend you to check if any unknown apps are authorized to access your account.
How to know if you are affected: If you open the "Authorized apps" menu of your user account, you can check if there are any applications that currently have access to your account. If an application is listed that you do not know about, an unauthorized attacher might have accessed your account. If you are a pretix customer, please reach out to us at security@pretix.eu in that case. If the list is empty or only contains applications you know about, you are not affected.
Severity rating: This security problem impacts login and authentication and has a potentially critical impact. At the same time, it can only be exploited in a very specific and rare scenario and any exploitation has a high chance of being detected. We therefore assess the severity of this issue as high.
Affected versions: pretix versions 1.16.0 until 4.17.0 are affected.
This issue has been found internally.
Fixed versions
All pretix installations are affected. We just released updates for the last three stable versions on PyPI that fix the problem. If you run a pretix installation older than 4.15, please upgrade to a recent version now.
The new docker images will appear on Docker Hub over the next few hours.
We strongly recommend that you always run the latest version of pretix, as every release contains useful and important bug fixes, even if they are not security related.
If you want to keep updated about bugfix and security releases, you should follow this blog closely. A RSS feed is available and we also announce every blogpost on twitter.
We take the security of our product very seriously and always go the extra mile to make sure you stay safe. As we are humans, security issues unfortunately still might occur from time to time. We do everything we can to find and fix them as timely as we can. If you notice any security problems or have any questions on this topic, please contact us in private at security@pretix.eu. We will always treat your message with the appropriate priority.